Active Focus
Modern attackers are both persistent and opportunistic. They will be looking for ways into your environment, continuously hoping to pry on mistakes, vulnerabilities and other opportunities.
To combat this, we developed Active Focus.
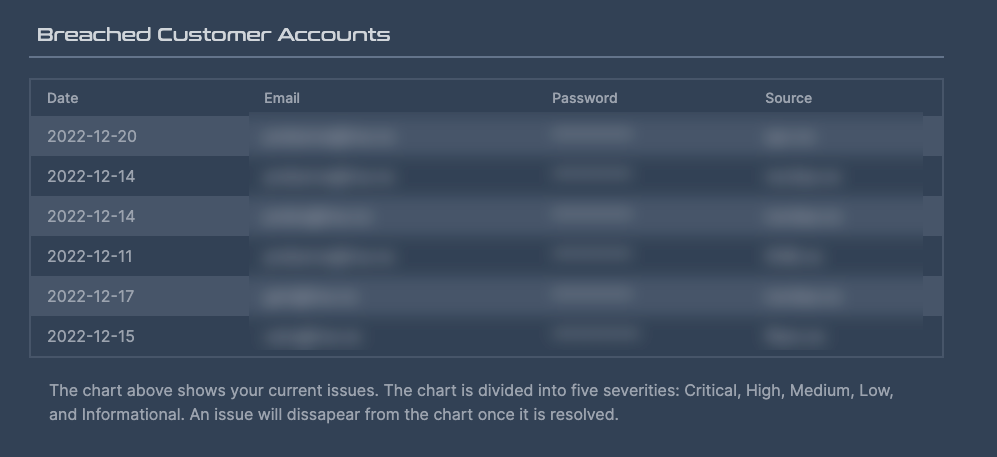
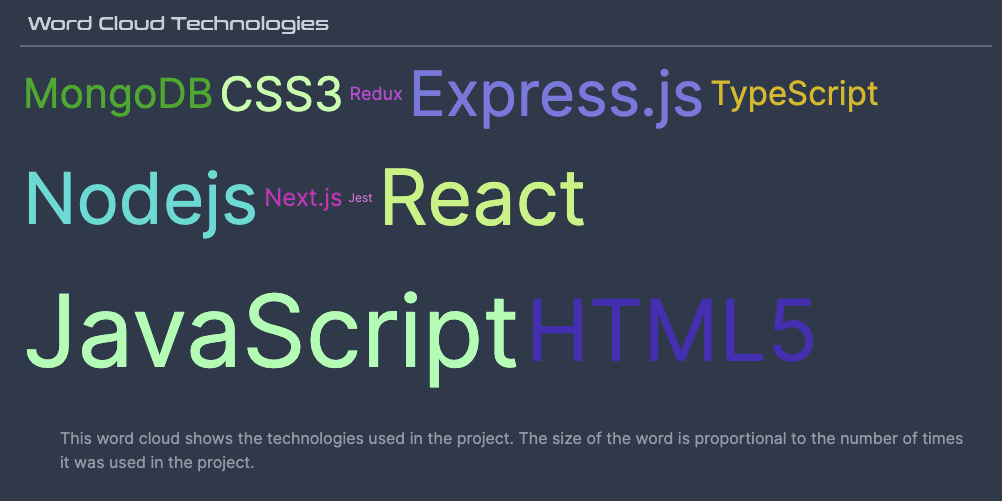
Active Focus is a comprehensive technology platform that features a variety of modules, including an Offensive Security Operating Centre. This combination of advanced technology and human oversight helps to ensure that our customers receive accurate and reliable information about vulnerabilities in their attack surface. By using Active Focus, our customers benefit from a robust and thorough approach to identify and address vulnerabilities before threat actors do.
What Active Focus Will Get You
The Solution
Traditional Penetration Testing is too slow. Cyber Criminals and other Threat Actors are rapidly running loops around our security teams. Security teams have a hard time prioritizing their time, understanding which risks need to be adressed, and what to fix, when and where!
This service challenges the existing methods of penetration testing and reactive security models, by defending forward. We are leaving our castle and the high walls we have built, and examining ourselves from the outside, in the perspective of a threat actor, finding holes and vulnerabilities before real attackers do. We call this Attack Surface Management and Always-On penetration testing.
Security organizations struggle with understanding how attackers operate, and how their organization becomes vulnerable over time. River Security is a razor sharp spear tip when it comes to offensive services, allowing us to provide our customers with relevant information on where security teams should prioritize.
We utilize ranges of Cyber Threat Intelligence, Penetration Testing techniques and much more to help ensure our customers can patch what is needed, when it is needed.

Our Customers Say It The Best
The team is very knowledgeable and has taught us a lot when it comes to proactive cyber security. They are agile and clearly has a lot of competence within their field, and we are happy to have them on our side in the ever-changing threat landscape.

One of the differentiating features of River Security is that they focus on real threats and areas that need attention – so we not only know about vulnerabilities, dark web disclosures and other issues, but also how they will affect our business.

...That’s where River Security comes in, offering their Active Focus service to keep us ahead of the curve with a constantly evolving attack surface, and even helping us to uncover the unknown...

How It Works
The Active Focus service is built on many components which enables our team to rapidly discover new attack surface, engage a team of penetration testeres and address risk as fast as posisble.
We developed a technology which gives us direct insights into what attackers see. When River Security's Offensive Security Operations Center receives an alert, it means an opportunity to attack our customer and help deal with immediate risks.
To achieve the necessary element of speed, correct information and actionability from our customers, we have developed a range of different modules that help us focus our attention at the right place, at the right time.
With the right people and the right technology, River Security is able to rapidly and effectively identify vulnerabilities and risk as they happen, in close to real time in many cases. It used to be the rabbit vs. the turtle, where the rabbit were the threat actors and the turtle was you and me, but we have finally taken back the advantage.
Explore How We Do It
Or see our page on how we fight cyber criminals
Steps To Better Security Hygiene
More About Our Service In These Selected Articles
Continuous Penetration Testing: Why Fresh Eyes Find Fresh Bugs
[Editor’s note: I wrote this short blog post to illustrate the advantages of Continuous Penetration Testing. In this case, a tester discovered a vulnerability triggered by a new event in Active Focus, even though the same issue had been missed during a previous test. It’s a great example of why continuous testing matters. ~Chris Dale]…
SSL/TLS Management: Reducing Risks and Gaining Visibility
Transport Layer Security (TLS) and its predecessor SSL remain cornerstones of modern internet security. They protect confidentiality, integrity, and authentication for data in transit. But while TLS is everywhere, managing it across an organization’s infrastructure is far from straightforward. Poor management introduces hidden risks that attackers are quick to exploit. Why TLS Management Matters For…
Pentesting is Transforming: 8 Steps to a Successful Pentest Operation in 2025!
Pentesting isn’t what it used to be, folks. Gone are the days of single checklist exercises and surface-level scans. In 2025, we’re transforming the way we think about pentesting—making it a dynamic, intelligence-driven, and collaborative practice that does more than just “find vulnerabilities.” We’re taking a proactive, adversary-informed approach that considers not only what’s in…