Mobile Apps Can Reveal Valuable Information for Attackers
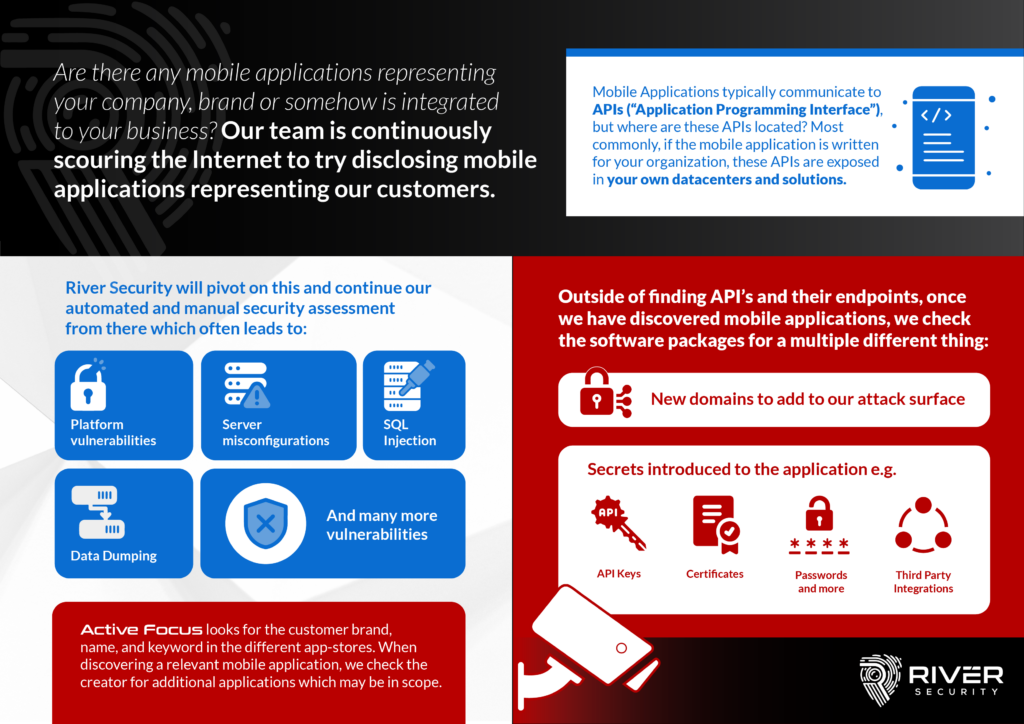
Mobile applications have become a crucial part of modern business operations, with many companies relying on them to connect with customers, manage internal processes, and handle sensitive information. However, the convenience and functionality of these apps also make them a potential target for attackers looking to gain unauthorized access to an organizations systems and data.
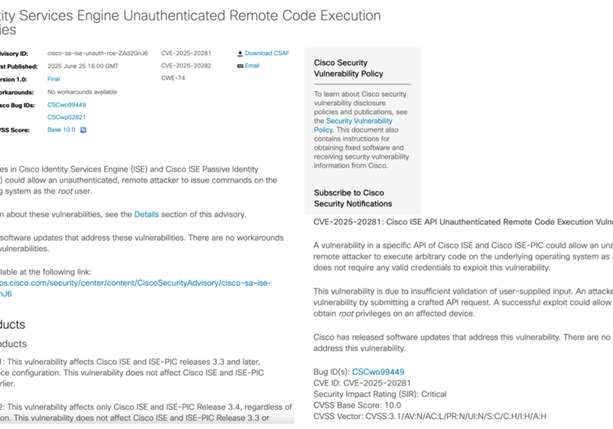
One common method for finding vulnerabilities in mobile applications is reverse engineering, which involves analyzing and deconstructing the app to understand its underlying code and functions. Reverse engineering can be used to identify security weaknesses and uncover hidden features or functionality that may not be immediately apparent to the user.
One of the primary benefits of reverse engineering mobile apps is the ability to discover secrets that may be hidden within the code. This can include things like API keys, certificates, passwords, and third-party integrations that could be exploited by an attacker. When River Security identifies company owned mobile applications, we reverse engineer them for secrets.
Reverse engineering can also reveal API connections to back-end data centers, which can provide an attacker with an avenue for attack through methods such as SQL injection or other vulnerabilities. In some cases, an attacker may be able to use these connections to gain access to sensitive information or otherwise disrupt the operation of the underlying systems.
Overall, the ability to reverse engineer mobile apps can be a valuable tool for identifying and addressing vulnerabilities in an organization’s security posture. By understanding the inner workings of these apps, River Security can help identify potential threats and ensure the security of our customers systems and data.