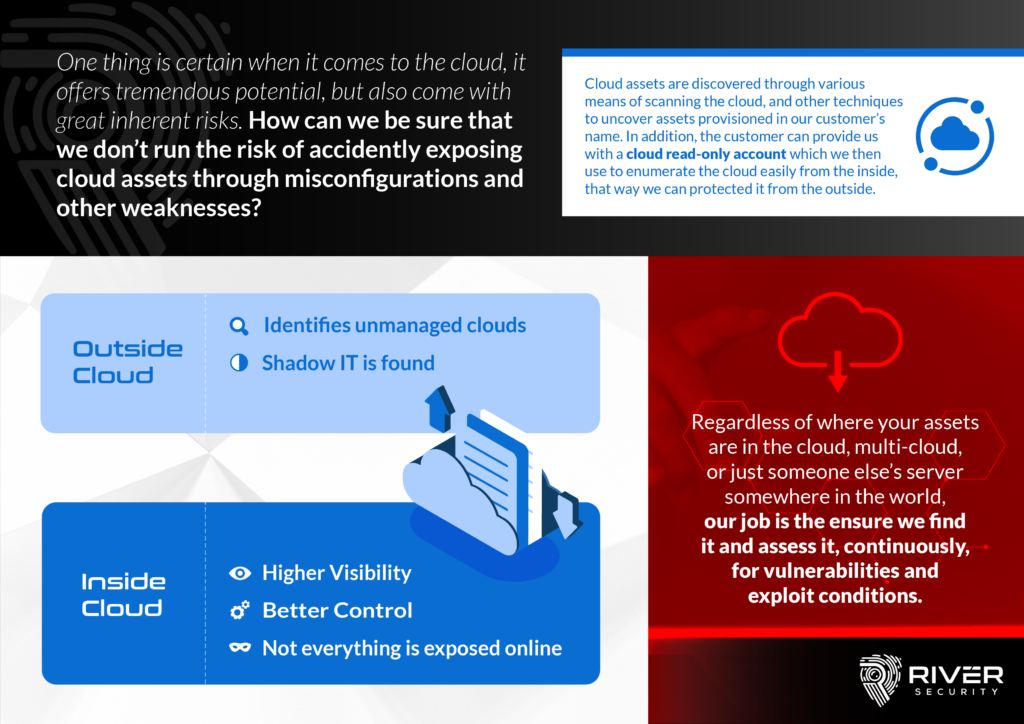
Cheating the Threat Actors: How River Security Monitors Cloud Assets to Stay Ahead
At River Security, we understand the importance of monitoring cloud assets in order to protect our customers from potential threats. That’s why we have developed a unique approach to monitoring these assets that involves not only scanning for them, but also using small pieces of code deployed inside customers cloud environments, fully controlled and operated by the customer.
By deploying these small functions in the cloud environment, we are able to receive direct insights into the deployed assets in our customers’ cloud environments. This gives us a significant advantage over other threat actors, as they are unable to access this information and are therefore at a disadvantage when it comes to identifying new or changed assets and being the first to find vulnerabilities.
One of the key benefits of this approach is that it allows us to monitor cloud assets more in real-time, ensuring that we are able to identify and respond to potential vulnerabilities as quickly as possible. This helps to minimize the risk of data breaches or other security incidents, and allows our customers to feel confident that their assets are being tested at all times.
By working closely with our customers to identify and address these vulnerabilities, we are able to help them build stronger, more secure cloud environments that are better able to withstand potential threats. Overall, our approach to monitoring cloud assets gives us a unique advantage in the fight against potential threats.