Code Repositories: A Wealth of Information and Potential Threats. How River Security Protects Your Assets
At River Security, one of our key priorities is helping our customers protect their assets and data from potential threats. One way we do this is by identifying customer-owned code repositories and looking for secrets that may be hidden within them.
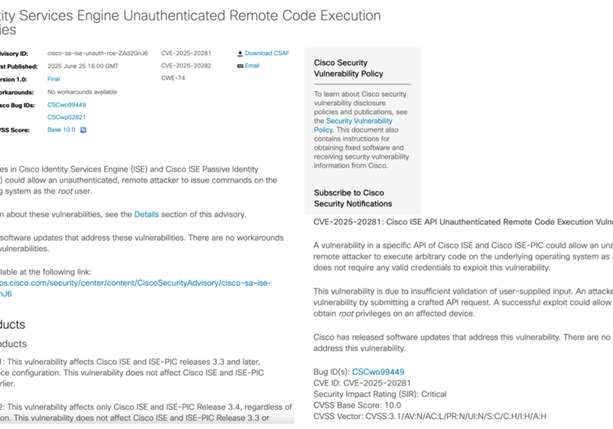
Code repositories can contain a wealth of information that is valuable to attackers, including references to other systems, secrets like certificates and passwords, and much more. By identifying these repositories and searching for secrets, we are able to help our customers protect their assets and data from potential threats. One of the key benefits of this approach is that it allows us to identify vulnerabilities in our customers’ systems and recommend remediation measures to address them.
In addition to identifying vulnerabilities, this approach also allows us to uncover valuable information that can be used to improve our customers’ security posture. For example, we may find references to other systems or third-party integrations that can be exploited by attackers, and recommend measures to secure these systems and prevent unauthorized access.
Our approach to identifying customer-owned code repositories and searching for secrets is an important part of our efforts to help our customers protect their assets, brand and data from potential threats.