Community
Content
All
- All
- Attack Surface Management
- Incident Response
- News
- Penetration Testing
- River Security
Welcoming Lucas Vanaheim – Senior Penetration Tester
We’re excited to welcome Lucas Vanaheim to River Security, where he joins us as a Senior Penetration Tester in our Offensive Security Operations Center (OSOC). Lucas brings experience from Norsk...
Continuous Penetration Testing: Why Fresh Eyes Find Fresh Bugs
[Editor’s note: I wrote this short blog post to illustrate the advantages of Continuous Penetration Testing. In this case, a tester discovered a vulnerability triggered by a new event in...
Welcoming Tomasz Czyz – Senior Penetration Tester
We are pleased to announce that Tomasz Czyz is joining River Security as a Senior Penetration Tester. Tomasz joins us from Atea, where he has worked as a Senior Security...
SSL/TLS Management: Reducing Risks and Gaining Visibility
Transport Layer Security (TLS) and its predecessor SSL remain cornerstones of modern internet security. They protect confidentiality, integrity, and authentication for data in transit. But while TLS is everywhere, managing...
Turning Cloudflare Into an SSRF Engine, Reaching What You Were Never Meant to See
[Editor note: Raymond identified a potential SSRF issue within Cloudflare infrastructure. While initially difficult to exploit due to limitations and unexpected behavior, further investigation confirmed real impact. By leveraging Cloudflare’s...
Welcoming Martin Nyberg – Penetration Tester
We’re excited to welcome Martin Nyberg to River Security, who joins us as a Penetration Tester in our Offensive Security Operations Center (OSOC). Martin comes from a strong technical background...
Welcoming Valdemar Andersen – Threat Intelligence Manager
We’re excited to welcome Valdemar Andersen to River Security, who joins us today as our new Threat Intelligence Manager. Valdemar comes to us from the role of Senior Cybersecurity Consultant...
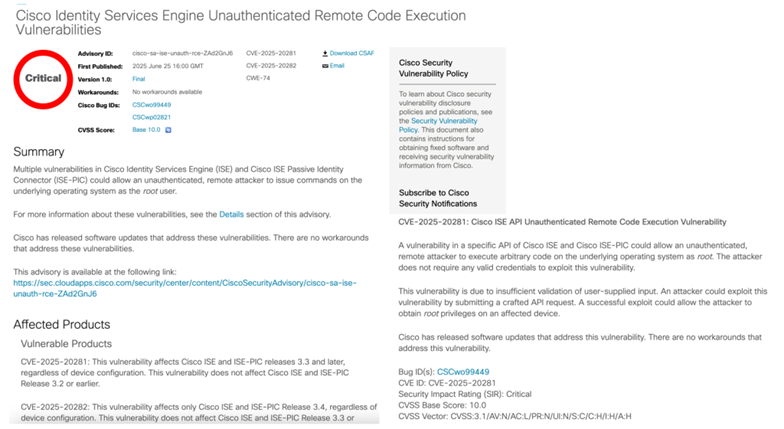
Like stealing (Cisco) ISE-cream from a kid – Weaponizing a CVE
[Editors Note: Raymond Strandheim is a principal pentester, and I asked him to share with us how he managed to weaponize a new vulnerability from Cisco into a working exploit...
From Norway to Sweden – with Europe in sight
Jens Dahlkvist (Country Manager Sweden, left) and Andreas Claesson (Principal Penetration Tester, right) With local leadership and senior expertise, we’re ready to meet the Swedish market River Security continues its...
Sikkerhetsfestivalen 2025: Reflections and the Road Ahead for Cybersecurity
Introduction What a festival. Sikkerhetsfestivalen 2025 – my first, and definitely not my last. The organizers and the city of Lillehammer brought together some of the sharpest companies and minds...