Penetration Testing
Continuous Penetration Testing: Why Fresh Eyes Find Fresh Bugs
[Editor’s note: I wrote this short blog post to illustrate the advantages of Continuous Penetration Testing. In this case, a tester discovered a vulnerability triggered by a new event in...
Why Cyber Due Diligence is Critical for M&A Success
[Editor's Note: Even Andreassen is one of our talented business developers. He is also an assistant professor at a Norwegian university. In this excellent blog post he has given us...
Pentesting is Transforming: 8 Steps to a Successful Pentest Operation in 2025!
Pentesting isn’t what it used to be, folks. Gone are the days of single checklist exercises and surface-level scans. In 2025, we’re transforming the way we think about pentesting—making it...
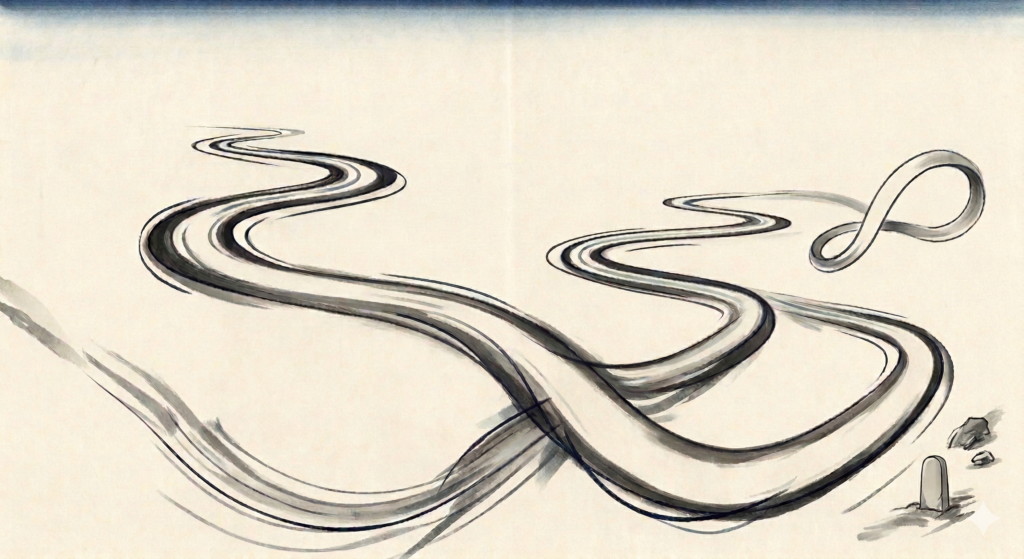
Penetration Testing Methodology – Much More Than Just Checklists
This blog post seeks to outline key aspects of the methodology River Security employs to identify vulnerabilities during our penetration testing. Our approach is continually evolving, designed to adapt to...
Finding Attack Surface and Other Interesting Domains via Certificate Transparency Logs
Certificate Transparency (CT) logs are like public records for internet security. When a new TLS certificate is issued, it gets logged in these CT logs. This makes it easier for...
Code Repositories: A Wealth of Information and Potential Threats. How River Security Protects Your Assets
At River Security, one of our key priorities is helping our customers protect their assets and data from potential threats. One way we do this is by identifying customer-owned code...
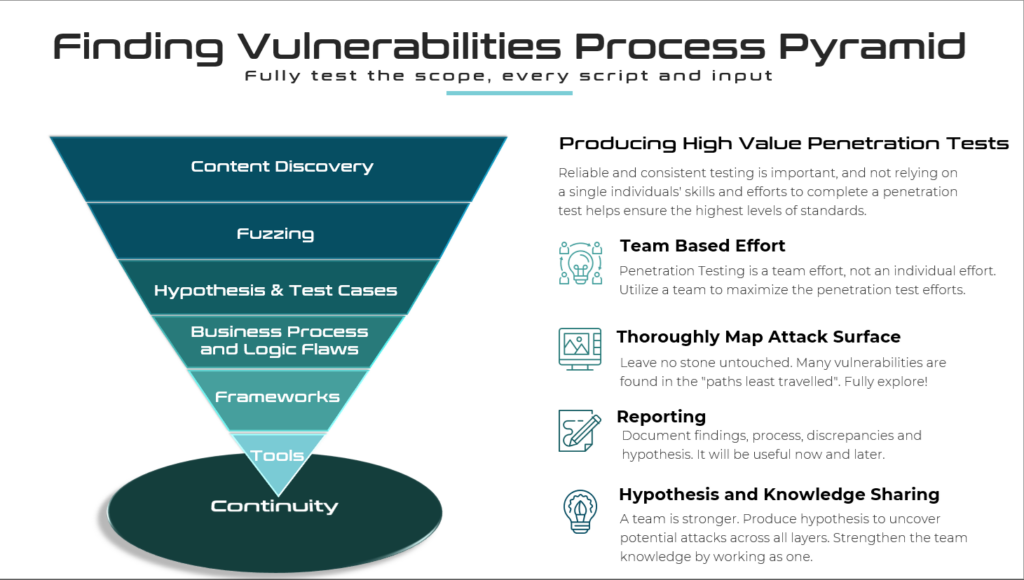
Cheating the Threat Actors: How River Security Monitors Cloud Assets to Stay Ahead
At River Security, we understand the importance of monitoring cloud assets in order to protect our customers from potential threats. That's why we have developed a unique approach to monitoring...
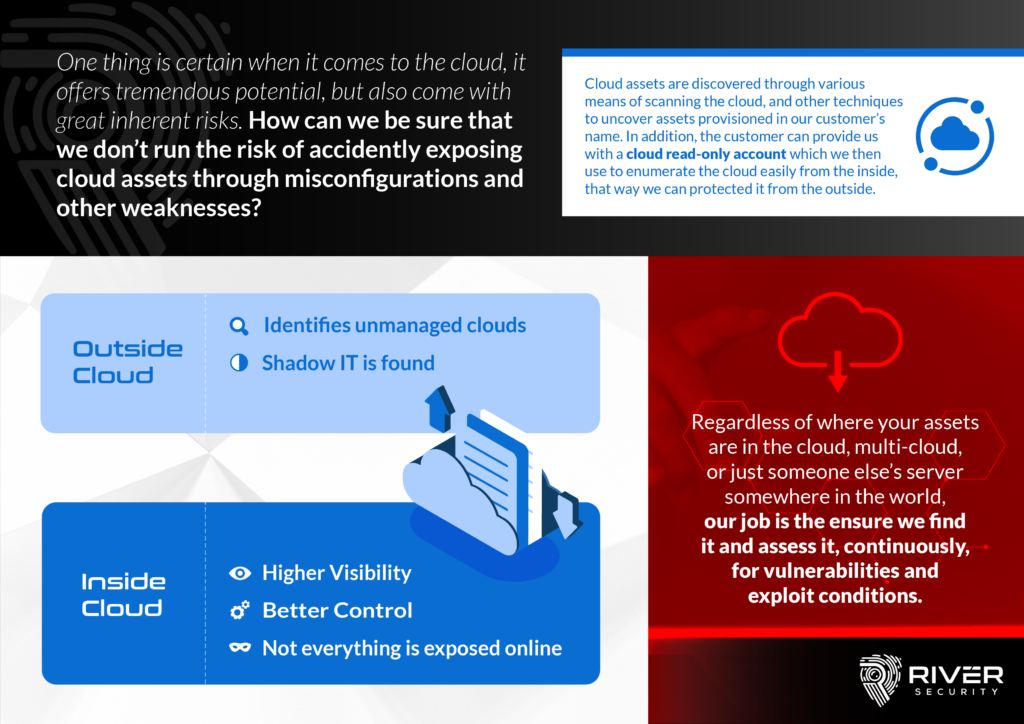
Mobile Apps Can Reveal Valuable Information for Attackers
Mobile applications have become a crucial part of modern business operations, with many companies relying on them to connect with customers, manage internal processes, and handle sensitive information. However, the...
Active Trace – Adding Deception to Aid Detection and Attack Surface Management
As the prevalence of cyber attacks continues to rise, it's more important than ever for organizations to protect themselves online. One tool that can help with this is Active Trace,...
Combating Digital Threats with Active Focus – Your Brand
Active Focus is designed to constantly monitor the digital attack surface of a business or organization, looking for signs of malicious activity or attempts to fraudulently use the company's brand....