Why We Monitor Technology
A key pillar in every organization
TECHNOLOGY
Why and how do we monitor it?
What kind of opportunities does it present our Offensive Security Operations Center?

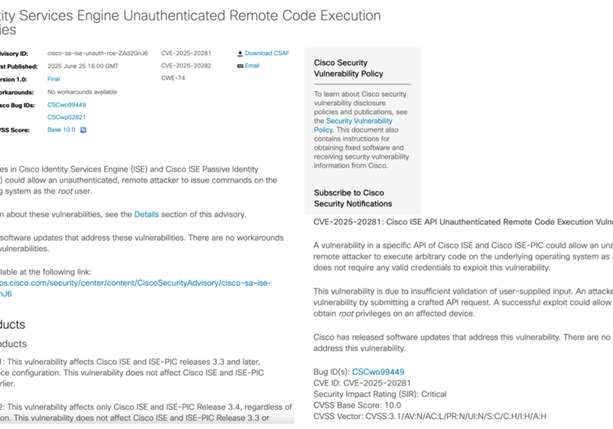
With aged technology comes vulnerabilities. These can in some cases, but far from every case, be exploited by attackers. Identifying technology as it dates, but also verifying if conditions are exploitable and presenting risk to the customer is incredibly important.
Our goal is to be the fastest and best threat actor, and as such we:
- Quickly and accurately identify different technology in our customers attack surface
- Classify the technology across a large number of classes, e.g. server operating systems, web frameworks and much more
- Analyze our findings and answer the question: Can we hack our customer now?
- Continuously stay on top of the technology, as it changes, to see if we can somehow break in tomorrow
Information from all our sources are normalized and presented to penetration testers to assess the situation. If we can not abuse a vulnerability in technology, we will not alert you about it. Present the information? Sure, but to alert? Nay, that would be crying wolf without being justified.
Through this module of our Active Focus delivery – we identify the different technologies in use by the customer. We produce extensive lists of all technology using scanners, OSINT vendors and commercial vulnerability management software. All this information is fed to River Security’s Offensive Security Operations Center (O-SOC) where it is processed and understood by our team.
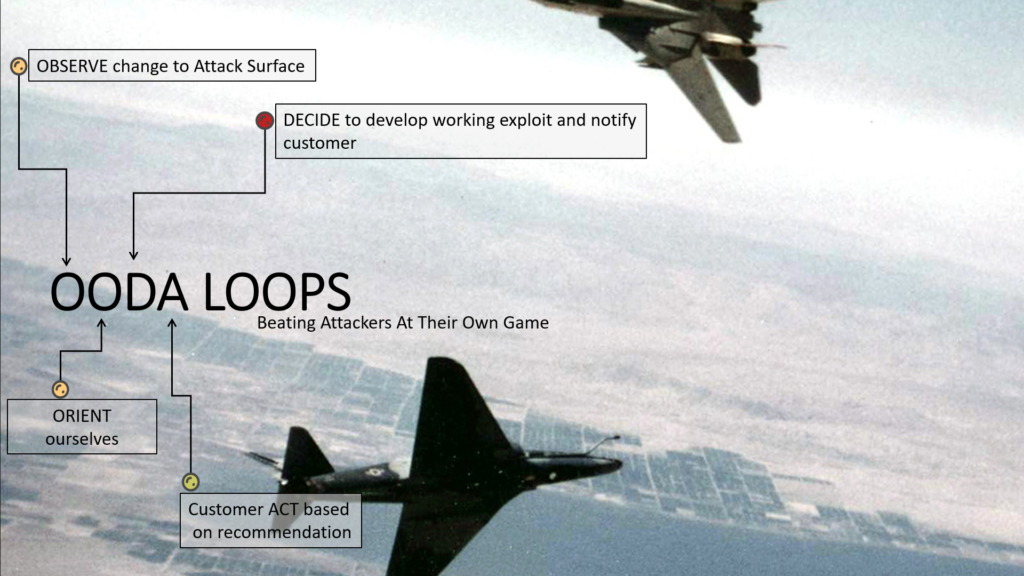
This model of operation, where risks are continuously assessed, opportunities to break in are always tested, and operating as close to cyber threat actors as possible, is the next generation of penetration test operations. Our Offensive Operations helps customers safe by being always-on, always looking and supporting our customers from an offensive perspective.