React faster to emerging threats
Modern attackers are both persistent and opportunistic. They will be looking for ways into your environment, continuously hoping to prey on mistakes, vulnerabilities and other opportunities. At River Security, we adopt the same approach, but with the goal of helping our customers by identifying and disclosing vulnerabilities before they can be exploited by malicious actors.
The value Active Focus brings you
About Continuous Attack Surface Management
Active Focus is a comprehensive technology platform that features a variety of modules, including an Offensive Security Operating Centre. This combination of advanced technology and human oversight helps to ensure that our customers receive accurate and reliable information about vulnerabilities in their attack surface. By using Active Focus, our customers benefit from a robust and thorough approach to identify and address vulnerabilities before threat actors do.
The Solution
Traditional Penetration Testing is too slow. Cyber Criminals and other Threat Actors are rapidly running loops around our security teams. Security teams have a hard time prioritizing their time, understanding which risks need to be addressed, and what to fix, when and where! This service challenges the existing methods of penetration testing and reactive security models, by defending forward. We are leaving our castle and the high walls we have built, and examining ourselves from the outside, in the perspective of a threat actor, finding holes and vulnerabilities before real attackers do. We call this Attack Surface Management and Always-On penetration testing.
Patch what is needed, when it is needed.
Security organizations struggle with understanding how attackers operate, and how their organization becomes vulnerable over time. River Security is a razor sharp spear tip when it comes to offensive services, allowing us to provide our customers with relevant information on where security teams should prioritize.
We utilize ranges of Cyber Threat Intelligence, Penetration Testing techniques and much more to help ensure our customers can patch what is needed, when it is needed.
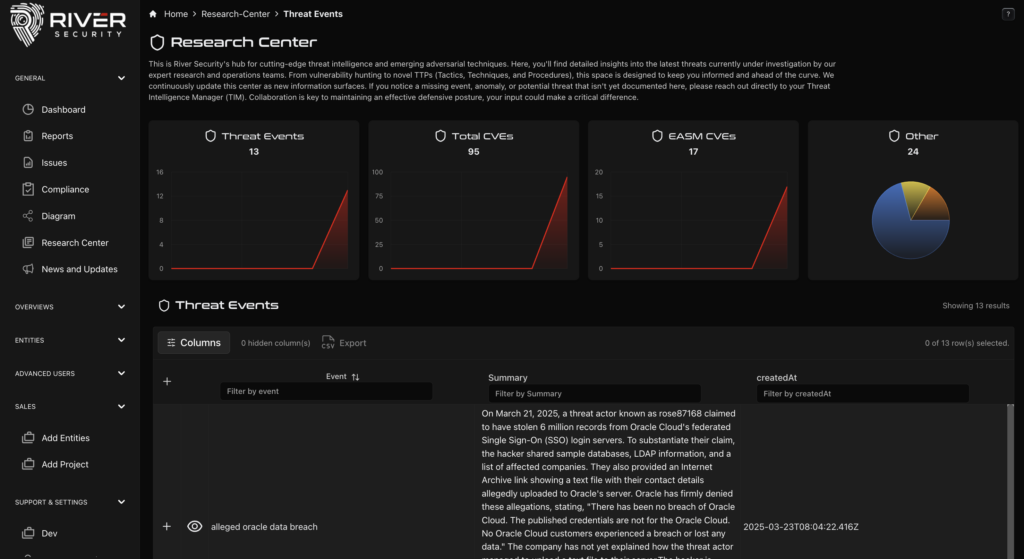
Our Offensive Security Operations Center
Where visibility drives action
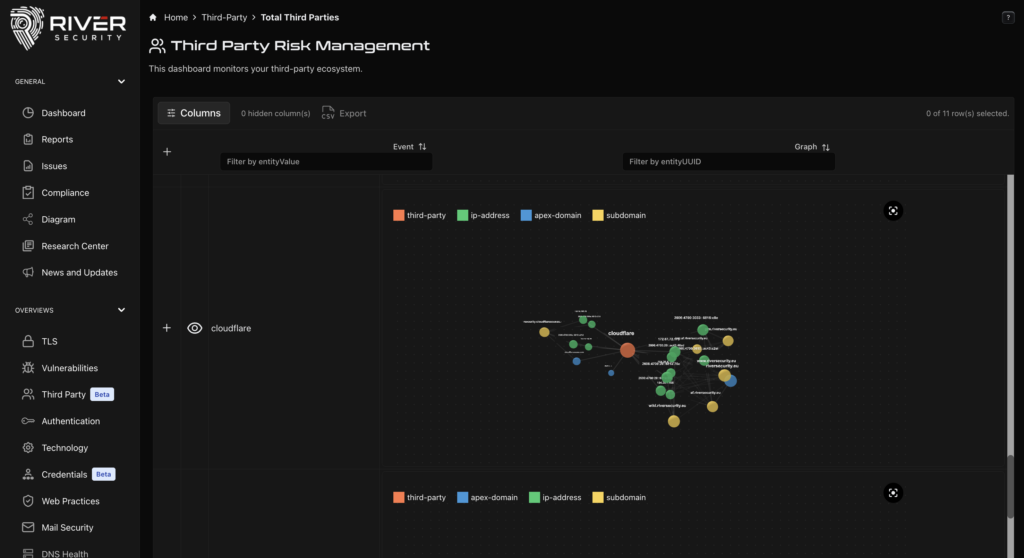
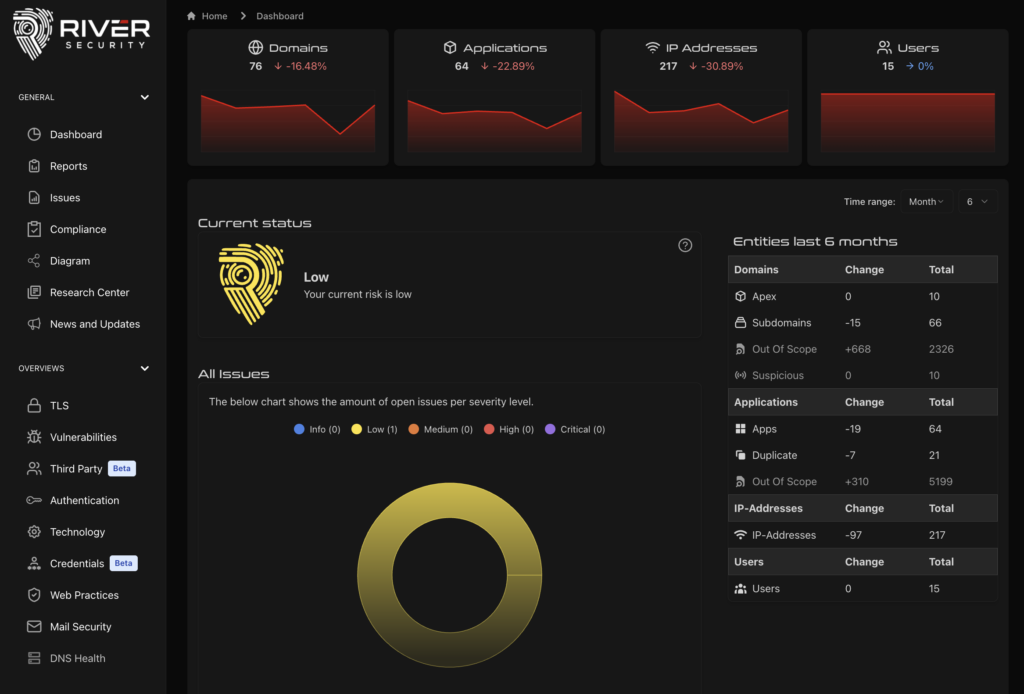
As we on-board, discover, scan and assess our customers, our Offensive SOC retrieves and stores large amounts of data. This data not only fuels the SOC, but allows our customers control in many different areas:
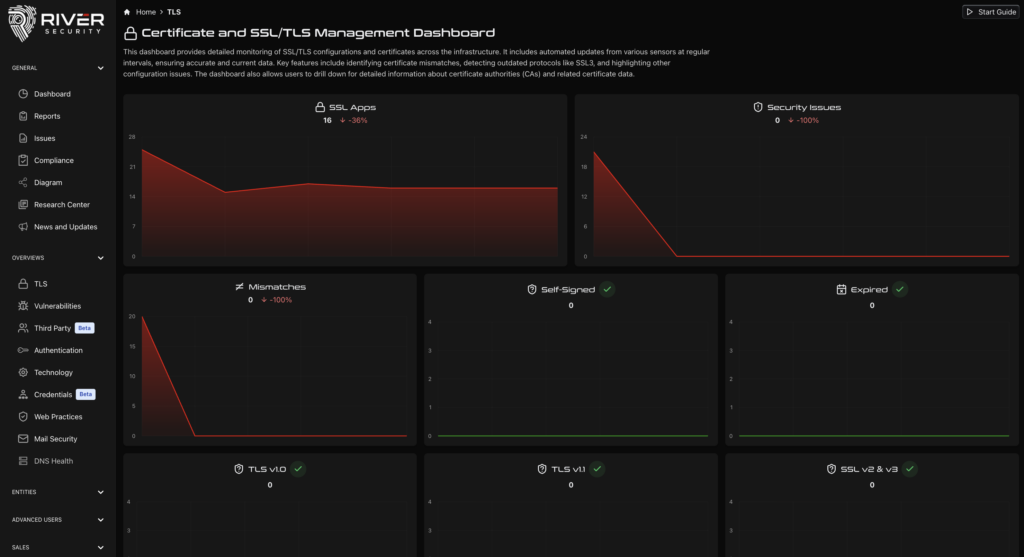
Certificate Management
We provide customers with information about which domains have expired certificates, which are due to expire, which Certificate Authorities are in use.
Vulnerability Management
What do scanners tell us about vulnerabilities present in our attack surface? River Security will report on exploitable issues, with demonstrations, but we also show you all the rest.
DNS Management
Seize control and start cleaning DNS. Find dangling DNS pointers, sub-domain takeover opportunities and improve your DNS hygiene.
Of course, there is more. Read How Attack Surface Management Empower Companies
The Process Behind Continuous Pentesting
The Active Focus service is built on many components which enables our team to rapidly discover new attack surface, engage a team of penetration testers and address risk as fast as possible.
We developed a technology which gives us direct insights into what attackers see. When River Security's Offensive Security Operations Center receives an alert, it means an opportunity to attack our customer and help deal with immediate risks.
To achieve the necessary element of speed, correct information and actionability from our customers, we have developed a range of different modules that help us focus our attention at the right place, at the right time.
With the right people and the right technology, River Security is able to rapidly and effectively identify vulnerabilities and risk as they happen, in close to real time in many cases. It used to be the rabbit vs. the turtle, where the rabbit were the threat actors and the turtle was the victims, but we have finally taken back the advantage.
Users of Active Focus

Active Focus Strengthens Sparebanken Vest’s Cyber Security Defense
“At the core of our comprehensive cyber-security approach is the concept of layered protection, ensuring that we are always at the forefront of the latest and greatest innovations in the industry. That’s where River Security comes in, offering their Active Focus service to keep us ahead of the curve with a constantly evolving attack surface, and even helping us to uncover the unknown. With a dynamic blend of cutting-edge technology and skilled expert verification, paired with lightning-fast agility, we are better equipped to tackle any threat that comes our way.”
Arvid Eriksen, CISO – Sparebanken Vest

How Mesta Reduced Cyber Security Risks with Active Focus
What we appreciate the most is the team’s expertise and their ability to provide both short-term and long-term solutions to any security challenges we face. It’s reassuring to know that every issue flagged in a report has been thoroughly vetted and verified by River Security’s team of experts, giving us the confidence we need to stay ahead of emerging threats.
-Terje Einar Hunvik, IT Operations Manager

Azets Chose Active Focus for Proactive Protection
“River Security’s Active Focus service has been a game-changer for us. It’s not just about identifying security issues; it’s about understanding how they affect our business. This service has significantly improved our IT security posture, and we now have the critical insights we need to protect our organization effectively.”
Ole-Martin Bekkeli, CISO – Azets

Aritma Secure Their Financial Data with Active Focus
“Engaging with River Security has transformed how we at Artitma approach our digital security landscape. It’s equivalent to expanding our IT department with an expert unit specialized in security, offering us continual vulnerability analysis that propels us forward with confidence and speed. The availability of extended penetration tests has been beneficial, highlighting the comprehensive support and value River Security brings to the table. It’s not just a service; it’s a partnership that secures our progress in the digital landscape.”
Kjetil Moklev Tollevsen, VP Products & Engineering – Aritma

Digiflow Increase Their Proactive Approach to IT-Security with Active Focus
“Choosing River Security as our offensive security partner has been a pivotal decision for us. The complex scope of our services, covering essential systems and cloud services for a growing clientele, naturally increased our exposure to cybersecurity threats. Such exposure required a strong defense strategy capable of proactively detecting and neutralizing threats, guaranteeing continuous service and preserving our clients’ confidence”
Erlend Bråten, Director of Operations – Digiflow

Travel Retail Norway Strengthens Cybersecurity with Active Focus After Cyber Attack
“Following the cyberattack we experienced in early 2024, we wanted to explore new ways to increase and strengthen our cybersecurity measures. We already employ a range of advanced solutions, but by choosing Active Focus from River Security, we have gained something new: The ability to efficiently map our entire externally exposed digital attack surface and continuously monitor, penetration test, and identify risks and hackable vulnerabilities on it. Our partnership with River Security helps us find and mitigate these before they can be exploited.”
– Linda Brenden, Chief Digital Officer, Travel Retail Norway