Posts by
Chris Dale
Continuous Penetration Testing: Why Fresh Eyes Find Fresh Bugs
[Editor’s note: I wrote this short blog post to illustrate the advantages of Continuous Penetration Testing. In this case, a tester discovered a vulnerability triggered by a new event in...
SSL/TLS Management: Reducing Risks and Gaining Visibility
Transport Layer Security (TLS) and its predecessor SSL remain cornerstones of modern internet security. They protect confidentiality, integrity, and authentication for data in transit. But while TLS is everywhere, managing...
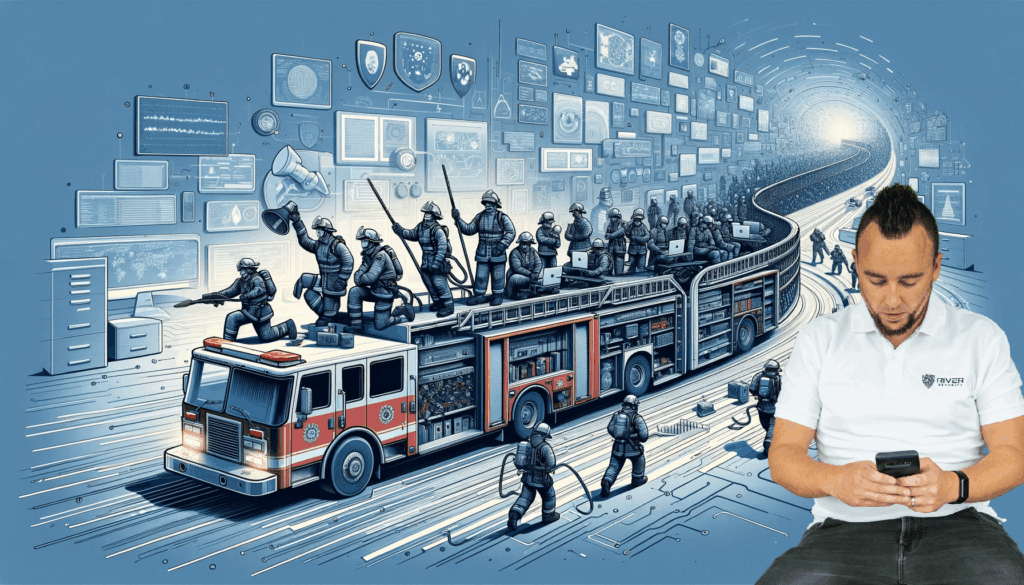
Pentesting is Transforming: 8 Steps to a Successful Pentest Operation in 2025!
Pentesting isn’t what it used to be, folks. Gone are the days of single checklist exercises and surface-level scans. In 2025, we’re transforming the way we think about pentesting—making it...
The Art of Discovery: A Penetration Tester’s Journey Through a Django Misconfiguration
[Editors Note: Eirik Valle Kjellby is an amazing gentleman and the latest, as of October 2024, addition to the ever growing penetration testing team at River Security. He continues to...
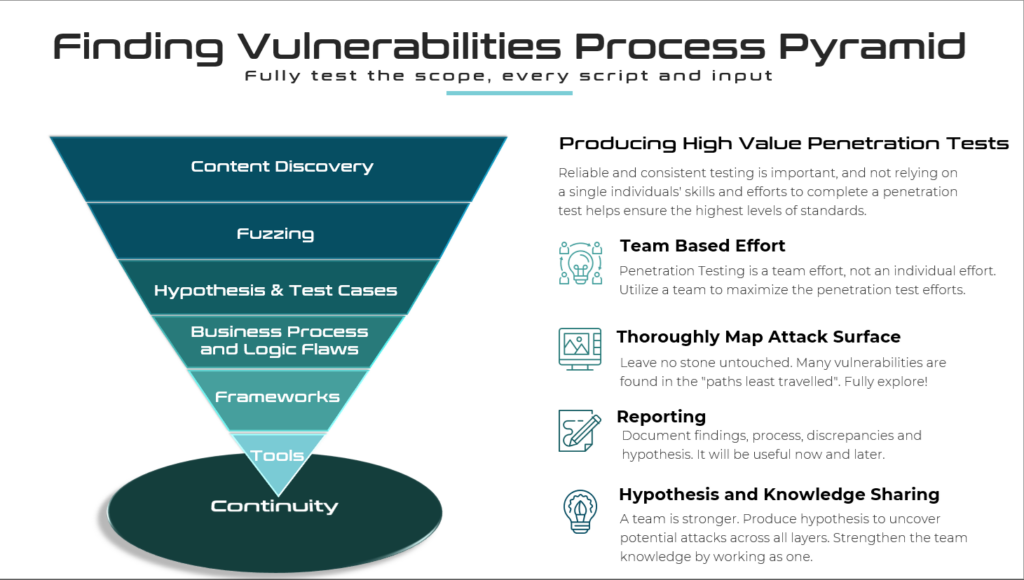
Penetration Testing Methodology – Much More Than Just Checklists
This blog post seeks to outline key aspects of the methodology River Security employs to identify vulnerabilities during our penetration testing. Our approach is continually evolving, designed to adapt to...
Finding Attack Surface and Other Interesting Domains via Certificate Transparency Logs
Certificate Transparency (CT) logs are like public records for internet security. When a new TLS certificate is issued, it gets logged in these CT logs. This makes it easier for...
Celebrating 4 Years of River Security: A Journey of Growth, Success and Stopping the Threat Actors!
As we celebrate our fourth anniversary, we at River Security are filled with immense pride and gratitude. What started as a small, ambitious venture has now grown into a robust...
The Penetration Testers Manifesto
This is River Security's ethos—our belief system, motivation, and inspiration. Interested in working with us? Check out our jobs page. As a hacker, I am driven by a relentless curiosity...
Ethical Considerations in Incident Response
Ethical considerations in incident response, especially when dealing with sensitive data and disclosing information about security breaches, are paramount. These situations require a careful balance between transparency, confidentiality, legal obligations,...
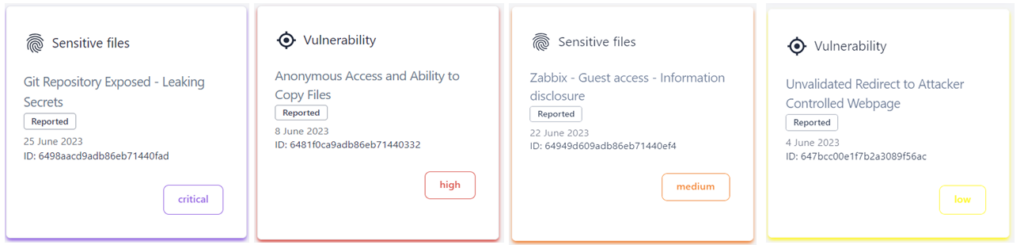
Distinguishing Vulnerabilities, Security Hygiene, and Exploitable Issues – Our Approach
In the ever-evolving landscape of cybersecurity, staying ahead of potential threats requires a keen understanding of the nuanced differences between vulnerabilities, security hygiene, and issues with demonstrable impacts on confidentiality,...