Distinguishing Vulnerabilities, Security Hygiene, and Exploitable Issues – Our Approach
In the ever-evolving landscape of cybersecurity, staying ahead of potential threats requires a keen understanding of the nuanced differences between vulnerabilities, security hygiene, and issues with demonstrable impacts on confidentiality, availability, or integrity. In this blog post, we’ll delve into how River Security sets itself apart by meticulously navigating these waters, offering a comprehensive approach to safeguarding digital assets.
Understanding the Terminology
Before we dive into River Security’s methodology, let’s clarify the terms we’re dealing with:
- Vulnerabilities: Weaknesses or gaps in a system’s defenses that could be exploited to compromise the integrity, availability, or confidentiality of information, often theoretically and exploit code is not avilable to threat actors.
- Security Hygiene: Best practices, policies, and measures implemented to maintain a healthy and secure digital environment. These are proactive steps taken to prevent vulnerabilities and ensure a robust defense.
- Exploitable Issues: Specific problems or weaknesses that, when exploited, have a tangible and demonstrable impact on the confidentiality, availability, or integrity of a system.
River Security’s Differentiation Strategy
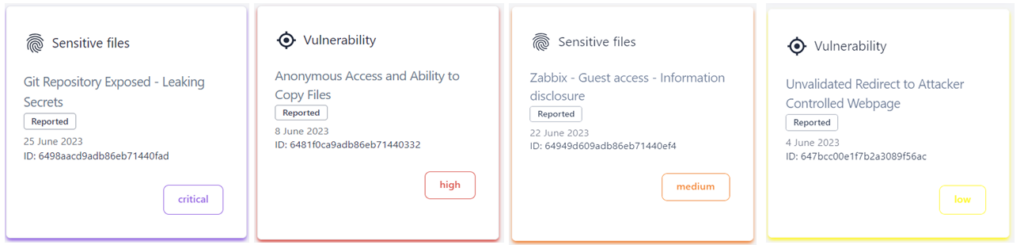
1. In-Depth Vulnerability Assessment: River Security employs a thorough vulnerability assessment process, actively scanning systems to identify potential weaknesses. However, the key differentiator lies in our ability to categorize these vulnerabilities based on their severity and potential impact. This does not only require automation, such as scanning and artificial intelligence, but also the human touch, the expert competency.
2. Security Hygiene Practices: Recognizing that prevention is often the best cure, River Security places a strong emphasis on proactive security hygiene measures. This includes regular system patching, enforcing strong access controls, and implementing robust security policies. By addressing these foundational elements, we fortify our clients against a multitude of potential threats. Our data is already collected to fuel our penetration testers, and while doing so, we can help our customers focus and prioritize other hygienic issues.
3. Risk Prioritization for Exploitable Issues: Not all vulnerabilities are created equal. River Security employs a risk-based approach to prioritize issues that have the potential to be exploited and cause real harm. This involves evaluating the likelihood of exploitation and the potential impact on critical business functions.
If there is a demonstrable effect on Confidentiality, Integrity or Availability, River Security goes beyond just identifying vulnerabilities; we focus on issues that can demonstrably affect our customers. Our approach ensures that efforts are directed towards mitigating threats that have a tangible impact on the core principles of information security, removing a lot of false-positives and time and efforts spent on the wrong areas.
The River Security Advantage
River Security stands out in the cybersecurity landscape by offering more than just a laundry list of vulnerabilities. Our approach combines proactive security hygiene practices with a nuanced understanding of the potential impact each vulnerability may have. By prioritizing issues with demonstrable effects on the CIA triad, we provide clients with a roadmap for effective risk management.
In conclusion, in the fast-flowing river of cybersecurity, River Security serves as a reliable guide, helping organizations navigate the complex waters of vulnerabilities, security hygiene, and exploitable issues. By adopting a strategic and risk-based approach, we empower our clients to stay ahead of the current and secure their digital landscapes effectively.