Breaking Into Information Security
People have continually been contacting me for mentorship, positions in their company or in general about how to get started in the Information Security industry. Thank you, I am honored. In my humble attempt to satisfy the latter, I have compiled a list of resources and some tips and tricks I often recommend to people getting started in this industry. First, let me tell you my story and a little bit about the industry.
From hotel room attendant to Head of Cyber Security and beyond
Before founding River Security (https://www.linkedin.com/company/river-security) I have been through many jobs requiring different skills and merits. I have always considered myself hard-working and my early career was not even related to IT in any way. I worked at hotels cleaning rooms, carrying luggage or cleaning dishes. I served 12 months military service and I have worked full-time as a tire repair man. Eventually I decided to become master of my own fate and make myself useful within IT: I decided to get myself a Computer Science degree.
I studied for my degree full-time during evenings while working as a service electrician at Rolls Royce, a rewarding and decent paying job I enjoyed, albeit having higher ambitions. I wanted to work full time with IT and more importantly with Information Security. During my final year of Computer Science study, I decided to leave my full-time job and work part-time as a tier-one helpdesk engineer for a Norwegian Internet Service Provider (ISP). This meant I got to focus more on my degree and I eventually landed a full-time job as a programmer with the same ISP after submitting my bachelor assignment; a software solution for said company.
After a couple of years as a developer I felt like I was on fire; I could do anything. Definitely experiencing the Dunner-Kruger effect. I was offered a job with IT-Operations which I bluntly turned down. Why would I change direction? I thought to myself that any good hacker would of course be a top-notch developer. I was not mature enough yet.
With years of experience as a developer, I could rise close to 80% proficiency in programming within the languages in question. The remaining 20% required to reach expert level would likely require 80% of my time or more, and to what end? My end-goal was a career in Information Security and that would probably not require expert-level programming skills. I suddenly realized that the IT-Operations job offer was the best opportunity that could ever land before my feet.
A week later, I decided to take the job with IT-Operations. It gave me great insights into how networks, middleware and applications operate and run. Knowledge which would be immensely valuable to any security professional. I started networking in the social arena, put my name in the hat for public speaking on ideas I had and eventually took security related courses.
Eventually I was offered a course with SANS and I was mind-blown by the talented instructor Steve Armstrong and by all the things I did not know from before. I studied heavily for the certification and eventually nailed it with a great score. This score triggered an automatic response from SANS asking me look into becoming an instructor. This was a huge opportunity that I could just as easily have missed. This new potential responsibility brought weight onto my shoulders and an expectancy that I could teach something to someone else. This caused me to step up my game even more, focusing, studying, and practicing harder to become an instructor.
While this was happening, I was promoted to different managerial positions and eventually landed a job as a CISO for a small Oil and Gas company in Norway. I realized I wanted to continue a more technical path and went on to do full time consultancy. After 5 years I was Head of Cyber Security at a mid-sized security consulting company in Norway.
This is when I took the next step founding something new. Read the story behind River Security here.
The InfoSec Industry
Information security is a great and challenging field to work in. It has a lot of great possibilities currently and I foresee even greater possibilities for the future. While this field really is truly awesome, it is also the Formula 1 of Information Technology. Everyone knows that IT is fast paced, but InfoSec is the fastest moving field in the industry. We need more people in this branch of IT, however there is not just a demand for head-count, but for SKILLED people. The skill gap is real and too many companies are putting “hats on heads”/”butts in seats”, often just to satisfy compliance requirements. Some companies are hiring without realizing the need for training or getting employees fully up to speed. Management who are not able to assess talent or perhaps more important, aptitude, will quickly realize that Information Security is not just an increasing cost-center, it also becomes a terrible return on investment (ROI). Further is a position where an employee is not expanding their knowledge nor improving their skills is not only boring and depressing, it can also be very damaging to the company. For instance, employees who mindlessly closes alerts due to lack of understanding and solely focus on a high solve-rate results literally in a company’s false sense of security.

How can you, as an aspiring InfoSec employee, seeking to penetrate the business, avoid becoming just another checkmark in a compliance requirement?
Level Up!
Having goals should also stimulate commitment in learning and preparing for reaching the goals. I have collected the resources that has been most valuable to me, and other things I consider might be helpful for you.
Books
Books are a great source for learning, except for those that ages rather quickly in an ever-changing industry. The books I recommend below are books I consider to be somewhat unaffected by time and serve as excellent primers on topics that are fundamental. I especially recommend the following books:
- Web hacking: The web application hackers handbook, Second Edition
- Exploitation: Hacking: The Art of Exploitation, Second Edition.
- Wireless: Hacking Exposed Wireless, Third Edition.
- Social Engineering: Social Engineering: The Art of Human Hacking
- Programming best practices: Code Complete: A Practical Handbook of Software Construction
Online Courses
There are many great online resources and courses on Information Security. Some are free, others not. Unfortunately, I do not have a tremendous amount of experience with free classes, but Google search results show ranges of free resources for you to get started, some even with accreditation. I would like to point out a few resources I do have experience with.
Cyber Aces from SANS is a free, easy to follow introduction to many topics within Information Security. As I represent SANS and know their quality, this one I can warmly recommend.

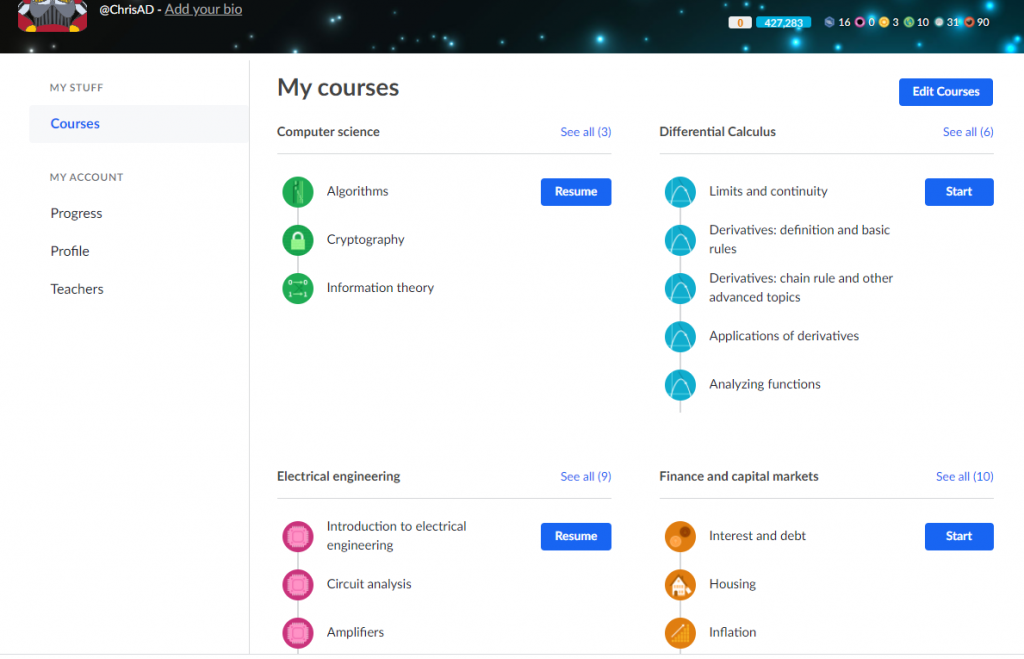
I have also used Khan Academy to brush up on some of my math skills, but they also have lectures in computer science and even some cryptography. khanacademy.org/#browse . I have been a longtime supporter of Khan Academy and I would wholeheartedly recommend you check them out.
Web- and Pod-casts
People are different in how they best acquire new knowledge. For some, optimal learning experience comes from watching videos, some prefer consuming the material through listening to talks/webcasts and others enjoy reading. Whichever person you are, hearing it from different sources in the industry can give you the insight you need to make your next step.
GIAC has an excellent podcast called “Trust me, I’m Certified” hosted by Jason Nickola. It features the topic on how to enter the industry with many industry experts featured on the podcast. Check it out here: https://www.giac.org/podcasts
Jason Blanchard, a former SANS colleague, and his wife have been hosting several webcasts, and even been featured in other podcasts, on the topic of job hunting and getting into Information Security. They also sometimes live-stream on Twitch – talking about the subject: https://www.twitch.tv/banjocrashland
John Strand and the crew at Black Hills InfoSec have been generating several webcasts on this topic, and one I would like you to watch is their “Your 5 Year Path: Success in Infosec“. A while later they developed a second version of the previously successful video.
Version 2 can be found here: https://www.blackhillsinfosec.com/webcast-john-strands-5-year-plan-into-infosec-part-2/
Lesley Carhart and Ean Meyer both created huge overviews on how to break through. Find Lesley’s “megamix” here, and Ean Meyer’s “Where should I start” here.
Challenge Yourself
Sometimes being stuck with a challenge, knowing there is a vulnerability and a solution, is a great way to learn, especially within the offensive side of security. Forcing yourself to Google, research, test and do proof-of-concepts are excellent ways to get ahead in the game.
If you are seeking to join the offensive side of Information Security, check out online hacking challenges like wargames and capture-the-flag (CTF) competitions. There are plenty of great challenges out there for both beginner and expert levels. In my opinion, these are great for learning. Make yourself familiar with sites and events like:
- overthewire.org
- wechall.net
- CounterHack and SANS’s Holiday Hack challenges.
- Hackthebox.eu
You can do write-ups and talk about your learning experiences during job interviews or while connecting with others in the business. This stuff works, and I can personally attest to it. I have hired two junior penetration testers from CTF challenges, and I have used CTF environments multiple times during interviews.
You do not have to set yourself up with a formal blog to get started in writing about your thoughts and experiences. A simple LinkedIn article might be everything you need to not only feel the waters, but to kick start many potential networking opportunities.
When stuck on a challenge, always exhaust all possible options and routes to success. Do not just go searching for someone else’s solutions. Perhaps you could replicate the target environment to better grasp the problem. A replicated environment also allows you to debug, manipulate code and analyze logs to further understand how a vulnerability can be exploited. Try to think of how someone else could have solved the challenge. Do not fool yourself looking for a shortcut to solve the challenge without first understanding the inner workings of how and why it behaves like it does.
Other Words of Advice
In the long run: Plan to work with IT-security, but don’t give up on chances to work with development or operations on your way there. The experience you will get is priceless.
When hiring people to whatever position, we humans would usually like to know as much as possible about the prospects in question. If you can show or tell (without breaking any NDA’s) previous work or research this will greatly help in satisfying employers need for knowledge regarding what you can bring to the company.
Try to think outside the box. Personally, I love people who can think new, especially trying to tie in user friendliness and usability with adequate and proper security measures.
Your day-job might not be very security related as you read this, but what stops you from discovering that relation? Always question security mechanisms and challenge them; try doing so without looking like a “know-it-all”, but instead shed a pragmatic and solution-oriented light on it. It is likely that your workplace currently has many challenges related to Information Security. Maybe you could approach those challenges with clever ideas? Push your insights and ideas in the direction of managers and people who care. Perhaps after a while you will be recognized as someone who is security conscious and interested, allowing you to pivot into InfoSec roles and climb the corporate ladders internally.
Apply social networking at events or through social media platforms. There are countless Slack workspaces, Discord servers and industry experts who will gladly take your questions via Social Media. Let people know of your ambitions and skill; do not be shy!
RTFM – Read the fine manual. I have had to do it on countless occasions. Many tools and systems come packed with great built-in help functions that can truly make you succeed in operating them.
Expect security controls to be in place, never become complacent. Where security controls are not present, investigate and report responsibly. Please be careful though and never do testing without the necessary permissions.
Most importantly, do not give up! We need you; it is just a matter of finding the right people with the right aptitude for Information Security. Be curious and patient. Do not expect shortcuts or immediate progression. Stick with your plan and be persistent! Do this and I am positive, you will become “the right person” turning yourself into a valuable asset to the industry.
Thank you for reading! With this, I encourage you to be curious and seek to understand something before attempting to make, break, exploit or fix it. With the right thirst for knowledge and right mindset, you can achieve anything anywhere. Good luck!



