How to engage a company in Offensive Services
This post will assist you in how to best start engaging a company in offensive services, because you want to understand the running risks of your company. It highlights how you can start by assessing your own digital footprint, then move into having penetration testing services on the assets identified as most critical.
Don’t start before you know your digital footprint
Most likely, you don’t know exactly how hackers operate, and that’s probably why you want to procure someone to aid you in understand where your risks are, and if they exceed your risk threshold or not. A good first step in engaging with a third party regarding offensive services is to first have them map your digital footprint; include physical assets too if that concerns you. Many penetration testing organizations can also do physical assessments, and River Security like to include that in foot printing efforts.
What can a digital footprint look like? It should include as many digital assets as possible, including but not limited to:
- Servers, IP addresses, domains, anything reachable over the Internet.
- Mobile applications, including endpoints relating to API’s.
- People, including any email addresses found, and what position they have at the company.
- Leaked credentials for any user in the organization.
Ideally, plot assets on map to better visualize your organizations digital footprint.
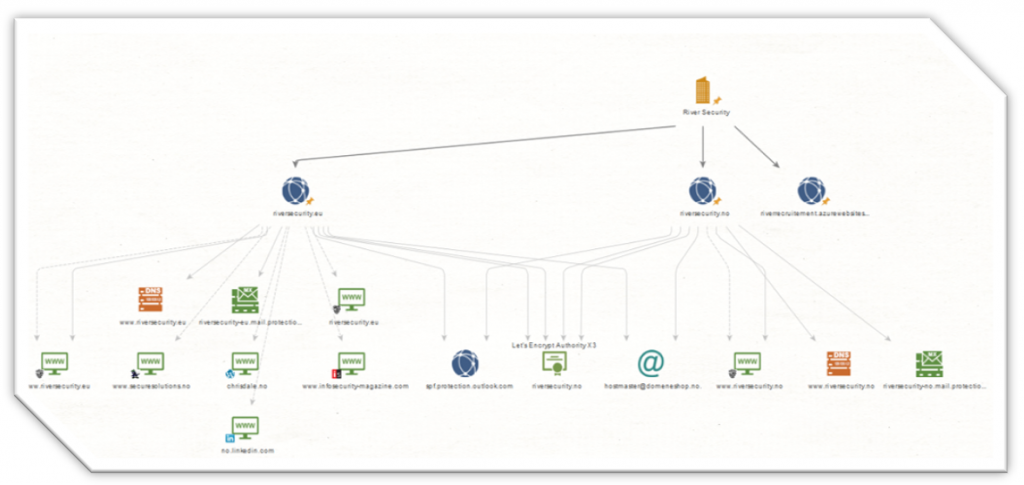
Such a digital footprint report should to the providers best ability disclose as many risks as possible, without performing any active exploitation penetration testing activities. Strictly should the behavior be non-hostile, relating to OSINT (Open Source Intelligence), Reconnaissance, Scanning and Discovery activities, most of which are considered harmless to the receiving end, and of which you’re already receiving amounts of already today.
Hand-over details, assess and start controlling the digital attack surface
Once someone has assessed your digital assets, it’s time to receive a report describing the results.
There are normally several things observed from assessing one’s own digital footprint which can give immediate value. There might be credentials that have been leaked, old systems that look unpatched and unmaintained or other things that you want to control. This is one of the beautiful things of allowing your partner first to map out the attack surface. You can now test the trust in the partnership with less upfront investments, and you also often get immediate and actionable results which will better prepare you for any impending penetration testing activities.
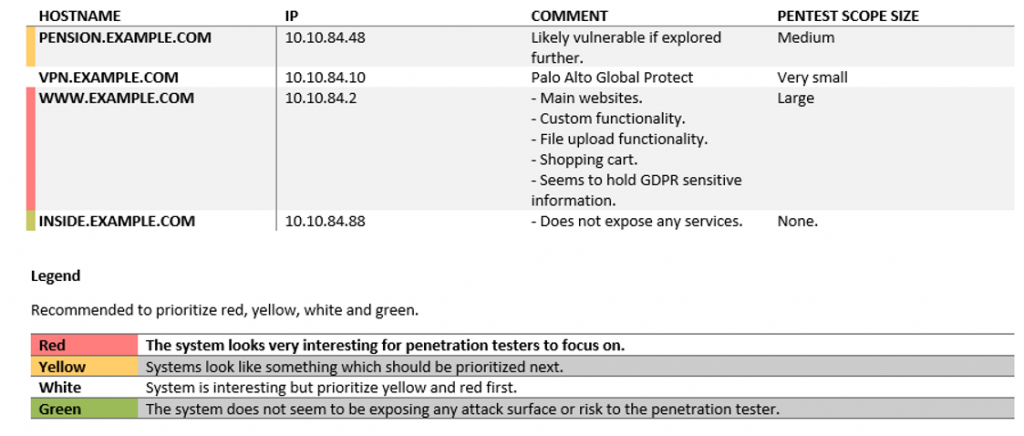
Ideally, the digital mapping exercise will leave you with a solid overview of an attackers’ perspective of your assets. An executive summary, or just a report summary depending on who the recipient is, should also conclude short- and long-term prioritization for the company. Any employees with leaked credentials, which you can address before any follow-up activities happen? Any vulnerabilities to be plugged? You should receive all this information in the results from the foot printing activities.
Furthermore, you probably want to act and ensure governance on a whole lot of things based on this report, e.g.:
- Social media accounts,
- shared emails,
- mobile applications,
- public cloud services.
Once you feel you’ve got a certain grasp of your digital footprint, then it’s time to put your systems to the test with a penetration test.
Where can I learn more?
River Security did a guest blog post at SANS, describing much more in details on how to start scoping offensive services, and what it should include. You can read it here: https://www.sans.org/blog/digital-footprint-offensive-services/