River Security
Pentesting is Transforming: 8 Steps to a Successful Pentest Operation in 2025!
Pentesting isn’t what it used to be, folks. Gone are the days of single checklist exercises and surface-level scans. In 2025, we’re transforming the way we think about pentesting—making it...
The Art of Discovery: A Penetration Tester’s Journey Through a Django Misconfiguration
[Editors Note: Eirik Valle Kjellby is an amazing gentleman and the latest, as of October 2024, addition to the ever growing penetration testing team at River Security. He continues to...
Guide to Navigate the Most Common Frameworks and Regulations for Cyber Security
In this comprehensive guide I will go through the most common frameworks and regulations for Cyber Security, as there might be some confusion in how to apply them to the...
Inside River Security’s Hacker Space in Austevoll
A couple of weeks ago, we packed our things at River Security and headed back to the beautiful Austevoll to participate in our semi-annual Hackathon, which we’ve named "Hacker Space."...
Welcome to the River Security team, Bjørnar!
We are excited to announce that Bjørnar has joined us as a Fullstack Developer, bringing a wealth of experience in programming, devops, and web development. At 27 years old and...
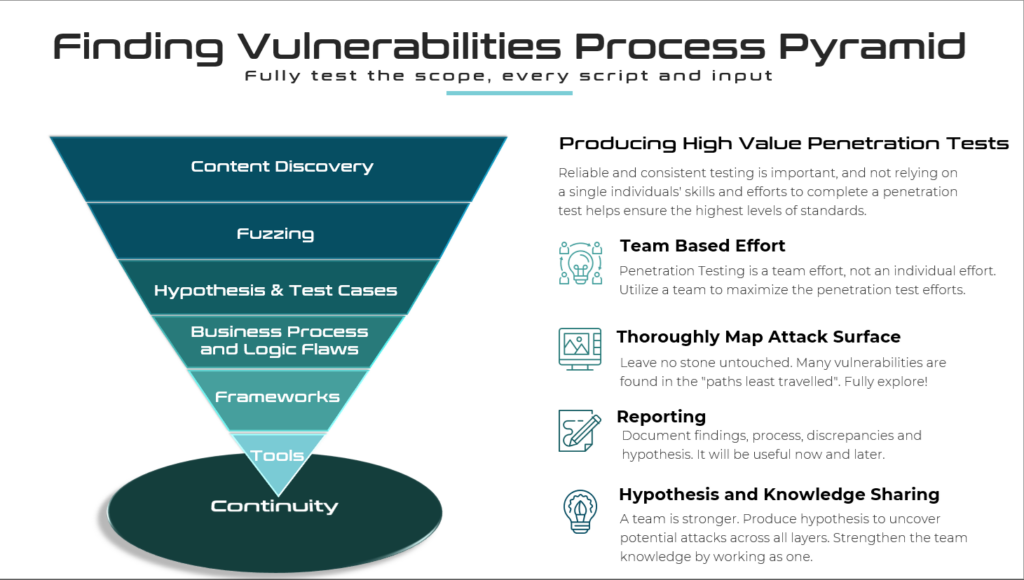
Penetration Testing Methodology – Much More Than Just Checklists
This blog post seeks to outline key aspects of the methodology River Security employs to identify vulnerabilities during our penetration testing. Our approach is continually evolving, designed to adapt to...
Depiction from B-Sides & DEF CON 32
This year’s B-Sides and DEF CON 32 were my first time ever going to the States and a hacking convention as large as DEF CON. Located in the Las Vegas...
Strategic Expansion: Knut Martin Hauge Joins River Security’s Board of Directors
We are proud to announce a key addition to our Board of Directors as we continue our journey of scaling and international expansion. Knut Martin Hauge joins us, bringing a...
Welcome to River Security, Eirik!
We are very happy to announce the newest addition to our River Security team, Eirik, who will hold the position of Offensive Security Engineer! With a strong passion for cybersecurity...
My First Weeks as COO at River Security
When I received the job offer to become the COO at River Security, I was thrilled, humbled, and super excited. I was joining a company with unparalleled expertise in cyber...